10 min read
Cybersecurity Challenges in Distributed Energy Systems: Securing the Smart Grid
In 2024, a SecurityScorecard report found that 90% of the world’s largest energy companies, including every top 10 U.S. power company, experienced...
Build intelligent, data-driven capabilities that turn raw information into insights, automation, and smarter decision-making across your organization.
Modernize, secure, and operationalize your cloud environment with solutions that strengthen resilience, reduce risk, and improve IT performance.
Deliver modern applications and connected IoT solutions that enhance operations, streamline workflows, and create seamless digital experiences.
High-impact IT project execution from planning to delivery, aligned with business goals and designed for predictable outcomes.
Structured change management and M&A support that helps teams adapt, reduce disruption, and successfully navigate complex transitions.
Cloud-first IT operations that streamline cost, strengthen security, and provide modern, scalable infrastructure for growing teams.
15 min read
Serverless Solutions Marketing Team : Updated on March 16, 2026

As energy companies modernize, the attack surface expands, exposing critical infrastructure to advanced persistent threats and insider risks. As per recent studies, unplanned downtime in a power plant can be extremely expensive. With losses exceeding $100,000 per hour, even a single incident can quickly escalate to more than $1 million in lost output.
The consequences of a successful attack can ripple across the entire energy supply chain, causing power outages, disrupting energy supply, and threatening public safety. With regulatory requirements tightening and the complexity of OT and IT environments growing, energy organizations must adopt a rigorous approach to vendor evaluation.
Evaluating cybersecurity vendors is no longer a routine procurement task; it is a strategic decision that determines the resilience and security of the entire energy grid. The process demands a blend of technical insight, regulatory awareness, and a deep understanding of the operational realities that define the power sector.
This Guide Covers:
P.S. Serverless Solutions brings deep expertise in securing energy infrastructure, combining always-on monitoring, rapid incident response, and regulatory alignment for OT and IT systems. Our cybersecurity experts help energy providers implement cybersecurity controls that protect against cyber threats, support compliance with evolving cybersecurity rules, and enable secure integration of new technologies like distributed energy resources and smart meters.
Book a strategy session to see how our cybersecurity services can help your energy company strengthen cyber resilience and reduce risk.
| Key Factor | What to Know and Do |
|---|---|
| Regulatory Alignment | Require vendors to provide NERC CIP audit support, SCADA policy documentation, and evidence of helping utilities pass regulatory reviews. Ask for sample audit reports and compliance playbooks. |
| OT/ICS/SCADA Experience | Insist on vendors with hands-on experience securing OT systems like PLCs in power plants, SCADA in grid substations, and DCS in oil and gas. Request case studies showing how they mitigated real-world attacks on these assets. |
| Risk Assessment & Management | Demand a risk assessment methodology that covers both legacy OT and modern IT, including vulnerability scans of control systems, supplier risk scoring, and quarterly risk reviews. Require sample risk assessment reports and remediation plans. |
| Incident Response & Resilience | Select vendors with documented incident response plans for OT environments, including escalation trees, regulatory notification templates, and post-incident root cause analysis. Ask for evidence of participation in sector-wide resilience exercises. |
| Visibility & Threat Detection | Look for solutions that provide automated asset discovery for all OT/IT devices, baseline network behavior analytics, and machine learning-based anomaly detection. Require a demo showing how their dashboard visualizes threats across the grid. |
| Contractual Provisions & Incentives | Include breach notification within 24 hours, vulnerability disclosure timelines, multi-factor authentication for remote access, and milestone payments tied to passing NERC audits or deploying secure smart meters. |
| Supply Chain & Third-Party Risk | Require continuous monitoring of supplier security posture, contractual obligations for incident participation, and supplier risk scoring. Ask for examples of how the vendor managed a supply chain breach in another utility. |
| Post-Deployment Risk Management | Schedule annual third-party audits, quarterly security reviews, and require vendors to provide post-incident feedback reports and updated risk management plans. Set KPIs for mean time to detect/respond and audit pass rates. |
The energy sector faces unique cybersecurity challenges that set it apart from other industries. Critical infrastructure such as power grids, oil and gas pipelines, and utility OT systems are frequent targets for advanced persistent threats and cyberattacks.
The convergence of operational technology and information technology, combined with the integration of Internet of Things devices, increases the complexity of the attack surface. Regulatory requirements like NERC CIP and SCADA standards demand strict compliance, while the consequences of a breach can disrupt energy supply, threaten national security, and endanger public safety.
Energy companies must evaluate vendors not only for technical capabilities but also for their understanding of regulatory frameworks, risk management best practices, and the operational realities of the energy industry. The right cybersecurity partner helps energy organizations protect against threats targeting critical operational assets and supports resilience across the entire energy infrastructure.
Read Next: How to Secure Cloud-Native Infrastructure in the Energy Sector
A structured evaluation process is essential for energy companies seeking effective cybersecurity. Vendors must demonstrate expertise in OT and IT environments, regulatory compliance, and the ability to address the unique risks facing the energy sector.
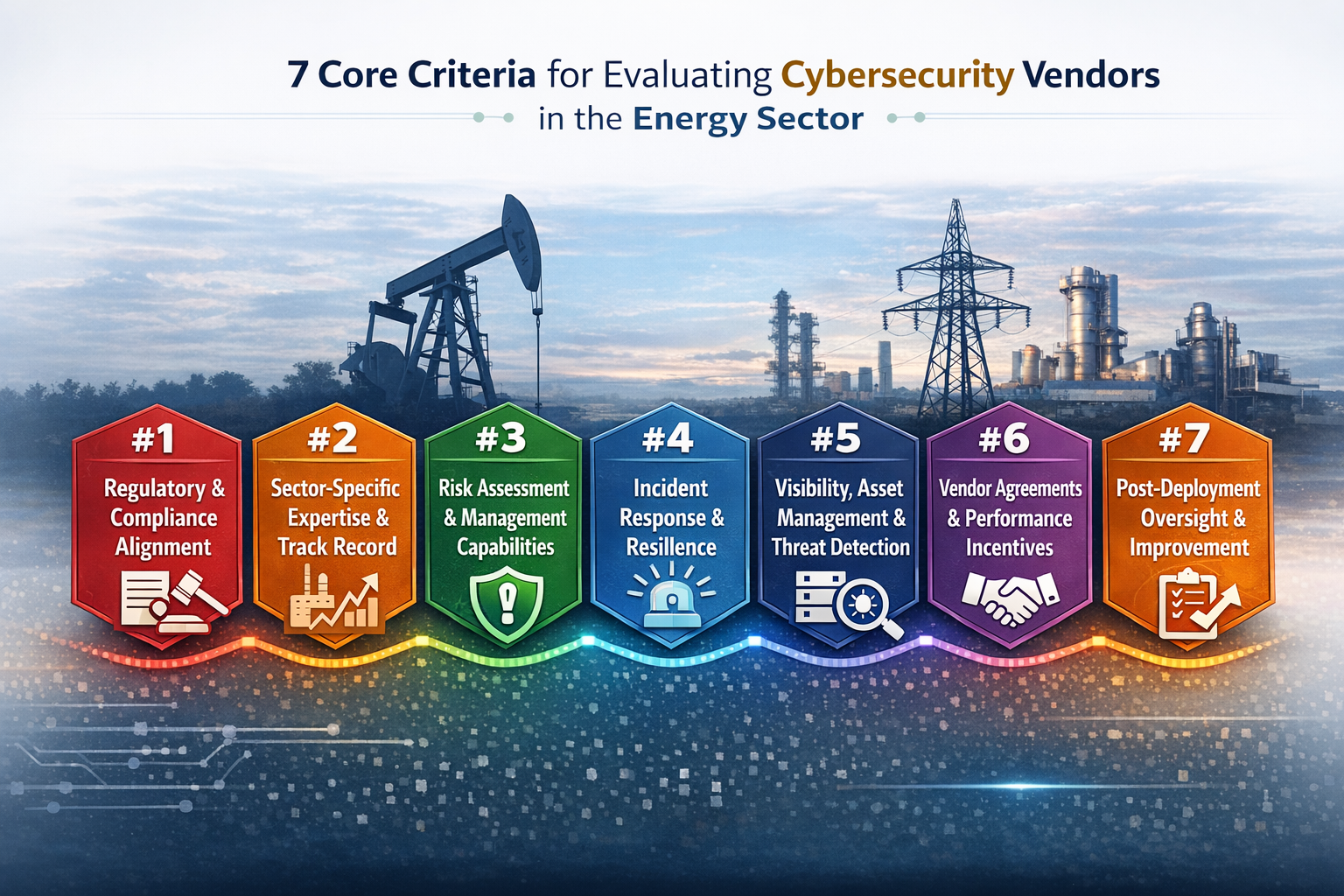
Regulatory compliance is a central requirement for cybersecurity programs in the energy sector. Any vendor supporting energy companies must demonstrate clear experience working with standards such as NERC CIP, as well as stronger security requirements specific to SCADA environments and operational technology (OT) systems. Vendors should be able to provide audit-ready documentation, assist with policy development, and support organizations during regulatory assessments and compliance reviews.
Energy companies should also confirm that vendors have practical experience helping utilities maintain compliance over time. This includes structured processes for updating security controls as cybersecurity standards and regulatory expectations evolve.
Organizations operating across multiple jurisdictions face additional complexity. Vendors must understand how to support both federal and state requirements, including frameworks such as TSA pipeline security directives and NRC nuclear regulations, while ensuring consistent protection across the broader energy system.
Compliance requirements will also continue to expand as the energy transition introduces new technologies across the grid. Electric vehicles, rooftop solar panels, battery storage systems, and other distributed energy resources are increasing connectivity across the power grid. Vendors must therefore show that their cybersecurity programs can extend to these emerging assets while maintaining protection for critical infrastructure and operational networks.
Read Next: Rethinking Cybersecurity: Turning Risk Into Strategy in the Energy Sector
A vendor’s experience in the energy sector is a non-negotiable factor. The complexity of OT environments, the prevalence of legacy control systems, and the unique threat landscape require specialized knowledge and proven results.
A comprehensive risk management approach is foundational for energy sector cybersecurity. Vendors should provide detailed methodologies for identifying, quantifying, and mitigating risks across both IT and OT domains, including the integration of distributed energy resources and deployment of smart meters.
| Risk Management Area | Vendor Capabilities and Requirements |
|---|---|
| Risk Assessments | Vendors must conduct in-depth risk assessments covering OT assets (e.g., SCADA, PLCs) and IT systems. This identifies vulnerabilities such as unpatched firmware, exposed remote access points, or insecure cloud services. Use frameworks like NIST CSF and NERC CIP for structured evaluation. |
| Vulnerability Management | Effective programs include regular scanning of OT networks, patch management for control systems, and prioritization of remediation based on operational impact. Vendors should provide quarterly vulnerability reports and actionable remediation plans for both hardware and software. |
| Supply Chain Risk | Assess how vendors evaluate third-party suppliers, including software or hardware providers. Require continuous monitoring and supplier risk scoring, with clear escalation paths for detected issues and supply chain attacks. |
| Continuous Monitoring | Vendors should deploy passive network monitoring tools that provide real-time alerts for anomalous activity in OT environments, including DERs and smart grid technologies. This enables early detection of cybersecurity threats targeting critical operational assets. |
| Reporting and Governance | Require vendors to deliver detailed, actionable reports aligned with regulatory requirements, including NERC CIP audit logs and incident documentation for compliance reviews and Department of Energy audits. |
Energy companies cannot afford delays or uncertainty during a cyber incident. Rapid response and the ability to restore operations quickly are essential for minimizing downtime and protecting public safety across the power grid and broader energy system.
For this reason, cybersecurity vendors should provide incident response plans specifically designed for operational technology (OT) environments. These plans should define clear escalation procedures and coordination protocols with internal security teams, regulators, and, when necessary, law enforcement agencies.
Effective vendors should also support post-incident investigation and recovery. This includes conducting root cause analysis, documenting incidents, and assisting with regulatory reporting required by energy sector cybersecurity standards.
Resilience planning is equally important. Vendors should help energy companies conduct regular tabletop exercises, implement reliable backup and recovery strategies for control systems, and align incident response with broader business continuity plans.
As distributed energy resources such as solar installations, storage systems, and other smart grid technologies become more common, incident response planning must also account for the risks associated with interconnected assets, automation platforms, and digitally managed energy infrastructure. Addressing these factors helps energy companies strengthen cyber resilience while maintaining the reliability of critical operations.
Maintaining visibility across all assets, especially in sprawling OT, IoT, and DER environments, is a cornerstone of effective cybersecurity. Vendors must deliver solutions that go beyond basic monitoring, offering deep insights into network behavior and advanced threat detection capabilities.
Robust contracts are essential for holding vendors accountable and ensuring ongoing alignment with operational and regulatory requirements. Agreements should include specific provisions for incident notification, vulnerability disclosure, and remote access controls. Performance incentive, such as milestone-based payments tied to successful audits or remediation, help maintain focus on measurable outcomes.
Energy companies often work with multiple suppliers across their technology and cybersecurity environments. Because of this, multi-vendor collaboration clauses are also important. These provisions establish clear coordination procedures during multi-party incidents and support the deployment of new cybersecurity controls across complex supply chains.
| Provision / Incentive | Vendor Requirement and Purpose |
|---|---|
| Incident Notification | Vendors must notify the organization within a defined timeframe (for example, 24 hours) of any breach affecting OT, IT, or cloud systems. Notifications should include incident details, affected systems such as control systems or smart grid infrastructure, and immediate containment steps to support regulatory reporting and incident response. |
| Vulnerability Disclosure | Vendors must promptly disclose vulnerabilities in vendor-supplied software or hardware. This should include severity classification, affected systems, recommended mitigations, and a defined timeline for patch deployment or temporary workarounds. |
| Remote Access Controls | Agreements should require strict controls for vendor remote access to control systems and operational networks. Examples include multi-factor authentication, time-limited access sessions, session logging, and approval workflows before vendors access sensitive environments. |
| Milestone-Based Payments | Vendor payments should be tied to measurable security outcomes such as passing a NERC CIP audit, completing deployment of secure smart meters or grid monitoring systems, or implementing an approved incident response plan. |
| Remediation Clauses | Contracts should require vendors to assist with remediation after a security incident. This may include deploying patches, supporting malware analysis, restoring affected systems, and assisting with regulatory documentation if an incident impacts energy infrastructure. |
| Multi-Vendor Collaboration | Agreements should define how vendors coordinate during incidents affecting multiple suppliers. For example, procedures may include shared incident response channels, coordinated forensic investigations, and defined communication protocols between vendors responsible for software, hardware, or cloud services. |
Ongoing vendor management is essential for maintaining a strong security posture as threats and regulatory requirements evolve. Energy companies should formalize oversight and improvement processes in their vendor relationships.
| Oversight Area | What to Require and Why It Matters | How to Execute and Measure |
|---|---|---|
| Annual third-party audits | Require independent assessors to review compliance with NERC CIP, SCADA, and OT controls. Validate that controls protecting control systems and grid operations are functioning as intended. | Schedule audits annually or semi-annually, review findings with vendors, and require remediation of gaps. |
| Quarterly security reviews | Vendors should participate in scheduled reviews to evaluate emerging cyber threats, update risk management plans, and assess whether security controls remain effective as infrastructure evolves. | Hold quarterly meetings, review updated risk assessments, and track progress on remediation actions. |
| Post-incident feedback | After any operational event or incident, require vendors to provide feedback reports, update risk management plans, and participate in structured review processes. | Conduct post-incident reviews, document lessons learned, and update incident response plans accordingly. |
| KPIs for success | Define metrics such as mean time to detect/respond, audit pass rates, vulnerability remediation timelines, and reductions in operational disruption or unplanned downtime. | Track KPIs in vendor dashboards, review during performance meetings, and tie contract renewals to results. |
Energy companies are navigating a period of rapid change, with digital transformation, supply chain complexity, and evolving threats all shaping the future of cybersecurity. These advanced considerations help organizations future-proof their vendor partnerships and maintain a strong security posture as the industry evolves.
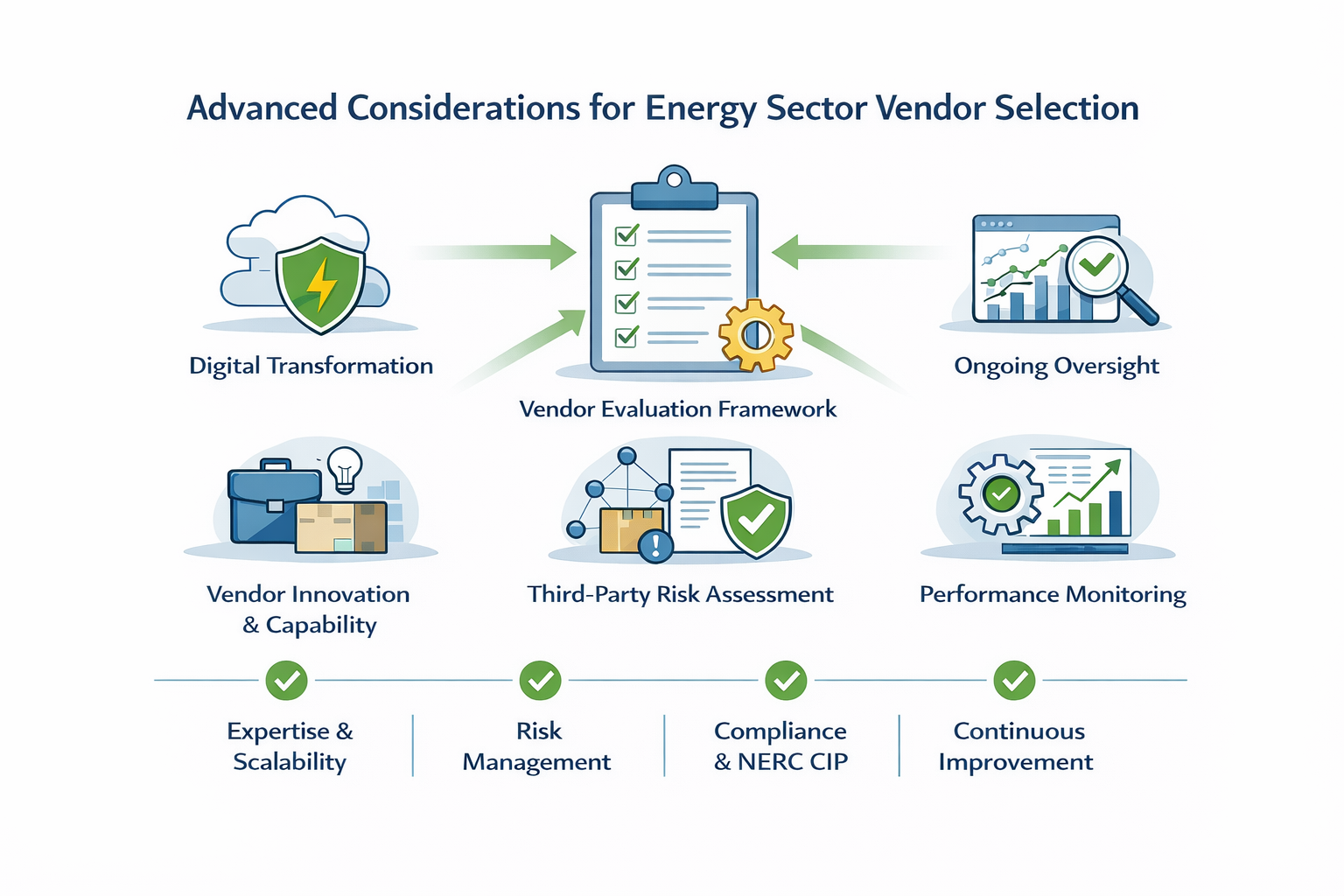
The energy sector is undergoing rapid digital transformation as smart grid technologies, renewable energy integration, and IoT-enabled operations expand across modern energy systems, reflecting the changing cyber risk landscape. As a result, cybersecurity strategies must also evolve alongside these changes to protect both traditional infrastructure and emerging digital platforms.
Vendors must demonstrate the ability to scale with digital transformation initiatives, supporting both legacy OT and new cloud-native platforms. This includes providing solutions that adapt to changing cybersecurity standards, enable secure integration of distributed energy resources, and support automation for faster incident response.
Future-proofing also means selecting partners who invest in ongoing research and development, ensuring their offerings remain effective against emerging threats targeting the energy and utilities sector, including electric vehicles, storage systems, and international energy interconnects.
The energy industry’s reliance on a vast network of suppliers introduces significant third-party cyber risks. Effective vendor management requires continuous monitoring, clear contractual requirements, and proactive incident coordination.
Energy companies should use tools that continuously track supplier cybersecurity posture rather than relying only on annual reviews. For example, monitoring platforms can track changes such as newly disclosed software vulnerabilities, expired security certificates, or signs of compromised credentials in vendor environments. These alerts allow security teams to address risks before they affect control systems or grid operations.
Organizations should apply structured risk scoring models to evaluate each supplier’s cybersecurity maturity. Factors may include whether the supplier maintains secure software development practices, uses multi-factor authentication for remote access, and regularly patches software and hardware used in energy infrastructure. Suppliers providing components for industrial control systems, smart meters, or grid management platforms should receive higher scrutiny because their systems interact directly with operational networks.
Suppliers should be required to follow recognized cybersecurity standards used in the energy sector, such as NERC CIP requirements for organizations supporting electric power system operations. Contracts should also require suppliers to maintain documented vulnerability management processes, including defined timelines for patching critical vulnerabilities in connected systems.
Energy companies should establish operational procedures that define how suppliers participate during a cyber incident affecting shared energy infrastructure. For example, suppliers responsible for grid monitoring platforms, SCADA-related software, or cloud-hosted analytics systems should have designated technical contacts who can support forensic analysis, system containment, and restoration of affected services.
Suppliers that support operational environments must also be prepared to assist with regulatory documentation. This may include providing security logs, vulnerability remediation records, and incident investigation reports required during compliance reviews related to energy infrastructure cybersecurity standards.
Cybersecurity in the energy sector requires continuous oversight. After a vendor is deployed, energy companies should verify that security controls remain effective through periodic audits, performance monitoring, and structured improvement processes.
These practices help ensure vendor solutions continue protecting control systems and operational environments as the energy system and grid infrastructure evolve.
| Post-Deployment Area | Vendor Expectations and Verification Activities |
|---|---|
| Post-Deployment Audits | Conduct annual or semi-annual audits of vendor systems and services supporting operational environments. Reviews should verify compliance with NERC CIP requirements, security controls protecting SCADA systems and OT environments, and the overall security of their systems. Independent third-party assessors can validate that controls protecting control systems and grid operations are functioning as intended. |
| Continuous Improvement | Require vendors to participate in scheduled security reviews (for example, quarterly). These reviews should evaluate emerging cyber threats, update risk management plans, and assess whether security controls remain effective as organizations expand infrastructure such as distributed energy resources or new grid technologies. |
| Feedback Loops | Establish structured review processes after operational events or incidents. Examples include post-incident reviews, security testing results, and feedback from system operators using vendor hardware and software. These reviews help identify operational gaps and guide improvements to deployed technologies. |
| Metrics for Success | Define measurable indicators to evaluate vendor performance. Typical metrics include mean time to detect and respond to incidents, audit pass rates, vulnerability remediation timelines, and reductions in operational disruption or unplanned downtime affecting power system operations. |
Even experienced energy organizations can fall into traps when selecting cybersecurity vendors. Recognizing and addressing these pitfalls is essential for building a resilient security posture.

Building a resilient cybersecurity program in the energy and utilities sector requires more than technical controls. Strategic alignment, cross-functional collaboration, and a commitment to continuous improvement are essential for staying ahead of evolving threats.
As there's an increase in regulatory scrutiny and sophisticated cyberattacks on energy infrastructure, organizations must adopt a proactive, structured approach to vendor evaluation and partnership. By focusing on sector-specific expertise, regulatory alignment, and ongoing risk management, energy companies can protect critical infrastructure and support operational reliability.
Before engaging with vendors, energy organizations should follow a clear, step-by-step process to ensure every aspect of cybersecurity is addressed.
Cybersecurity in energy organizations requires coordination across IT, OT, procurement, and executive leadership. Establishing shared objectives and governance structures helps ensure that security initiatives align with operational priorities.
Regular communication between teams, joint risk assessments, and cross-functional training exercises can improve incident response readiness and strengthen organizational resilience.
Engaging stakeholders early in the vendor evaluation process also helps organizations make informed decisions, reduce implementation delays, and support continuous improvement across cybersecurity programs.
Read Next: Shadow AI: Things to Consider When Your Executive Team is Feeling Vibe-y
Securing the energy and utilities sector against advanced cyber threats requires a deliberate, multi-layered approach to vendor evaluation. By focusing on regulatory alignment, sector-specific expertise, risk management, and continuous improvement, energy companies can build a cybersecurity program that protects critical infrastructure and supports operational reliability.
The journey does not end with vendor selection. Ongoing collaboration, regular audits, and a commitment to resilience are essential for staying ahead of evolving threats.
As the energy sector faces increasingly complex cyber threats and regulatory demands, having a trusted partner with deep industry expertise can make all the difference. Serverless Solutions delivers cybersecurity services designed specifically for energy companies, combining 24×7 monitoring, rapid incident response, and compliance support for OT, IT, and cloud environments.
Book a strategy session to explore how our tailored approach can help your organization achieve stronger cyber resilience, meet evolving standards, and safeguard your critical infrastructure.
Energy companies must comply with a range of regulations, including NERC CIP for bulk power systems, TSA pipeline security directives for gas and hazardous liquid pipelines, and NRC requirements for nuclear facilities. These frameworks mandate controls for OT and IT environments, incident response, supply chain risk management, and regular audits. Non-compliance can result in significant financial penalties and increased scrutiny from regulators.
Assessing OT security expertise involves reviewing the vendor’s experience with SCADA, DCS, and PLC systems, as well as their track record in managing incidents affecting critical infrastructure. Request detailed case studies, technical references, and proof of successful deployments in similar environments. Conduct technical demonstrations and evaluate the vendor’s ability to integrate with legacy and modern OT assets, including smart grid and distributed energy resources.
A robust contract should specify incident notification timelines, vulnerability disclosure requirements, remote access protocols, milestone-based payments, remediation support, and multi-vendor collaboration procedures. Include clauses for regulatory compliance, audit support, and performance metrics tied to detection, response, and uptime, especially for new cybersecurity deployments.
Managing third-party cyber risks requires continuous monitoring of supplier security posture, quantitative risk scoring, and clear contractual requirements for compliance and incident reporting. Establish joint response protocols with key suppliers and require regular documentation for regulatory audits. Use automated tools to track changes in supplier risk levels and prioritize remediation efforts, especially for software and hardware connected to the internet.
Strong vendors demonstrate deep OT/ICS expertise, a proven incident response history, regulatory fluency, and the ability to provide unified visibility across IT and OT environments. Look for partners who offer continuous improvement plans, participate in sector-wide resilience exercises, and maintain transparent communication throughout the engagement, especially as new technologies are deployed.
Vendor performance should be reviewed at least annually, with additional reviews after major incidents or regulatory changes. Schedule regular audits, quarterly review meetings, and post-incident feedback sessions to ensure ongoing alignment with operational and compliance requirements. Use defined KPIs to measure effectiveness and drive continuous improvement, especially as the energy system evolves.

10 min read
In 2024, a SecurityScorecard report found that 90% of the world’s largest energy companies, including every top 10 U.S. power company, experienced...

9 min read
A single cyber incident can disrupt power for hundreds of thousands, as seen in the 2015 Ukraine grid attack that left 225,000 people without...
6 min read
CIOs and CISOs in the energy sector are facing an inflection point. As digital infrastructure expands across operations, supply chains, and control...